156-315.80 – Check Point Certified Security Expert (CCSE) R80.40 – Updated 2021
За Курса (About this Course):
-
- Advanced three-day course teaches how to build, modify, deploy and troubleshoot Check Point Security Systems on the GAiA operating system. Hands-on lab exercises teach h ow to debug firewall processes, optimize VPN performance and upgrade Management Servers. Validate and enhance your skills and optimally manage Check Point advanced security management systems.
Цели – Какво ще научите (Course Goals/Skills):
- Articulate Gaia system management procedures.
• Explain how to perform database migration procedures.
• Articulate the purpose and function of Management High Availability.
• Describe how to use Check Point API tools to perform management functions.
• Articulate an understanding of Security Gateway cluster upgrade methods.
• Discuss the process of Stateful Traffic inspection.
• Articulate an understanding of the Check Point Firewall processes and debug procedures.
• Describe advanced ClusterXL functions and deployment options.
• Explain how the SecureXL acceleration technology enhances and optimizes Security Gateway performance.
• Describe how the CoreXL acceleration technology enhances and improves Security Gateway performance.
• Articulate how utilizing multiple traffic queues can make traffic handling more efficient.
• Describe different Check Point Threat Prevention solutions for network attacks.
• Explain how SandBlast, Threat Emulation, and Threat Extraction help to prevent security incidents.
• Recognize alternative Check Point Site-to-Site deployment options.
• Recognize Check Point Remote Access solutions and how they differ from each other.
• Describe Mobile Access deployment options.
Курсът е предназначен за (Audience):
- Technical professionals who perform advanced deployment configurations of Check Point products.
Формат на курса

Език на курса: български (английски е наличен като опция)
Учебни Метериали: в електронен формат (Учебните материали са на английски), включени в цената с неограничен достъп.
Лабораторна среда: всеки курсист разполага със собствена лаб среда, където се провеждат упражненията, част от курса.
Продължителност
- 3 работни дни (09:00 – 17:00)
или
- 24 уч.ч. обучение (теория и практика) в извънработно време с продължителност 2 седмици
- събота и неделя 10:00 – 14:00, 14:00 – 18:00, 18:00 – 22:00
- понеделник и сряда 19:00 – 23:00
- вторник и четвъртък 19:00 – 23:00
Плащане
If you are Check Point Partner you can also get free training via the Co-op Program. Check your eligibility and request funds here or For any further questions or additional assistance, please E-Mail: [email protected]
Заявка за издаване на фактура се приема към момента на записването на съответния курс.
Фактура се издава в рамките на 7 дни от потвърждаване на плащането.
Предстоящи Курсове
За повече информация използвайте формата за контакт.
Ще се свържем с Вас за потвърждаване на датите.
Предпоставки (Изисквания) за Участие (Prerequisites):
-
-
- Security Administration Course or CCSA certification (R80 Not R77)
- Windows Server, UNIX and networking skills and TCP/IP experience
- Certificate management and system adminstration
-
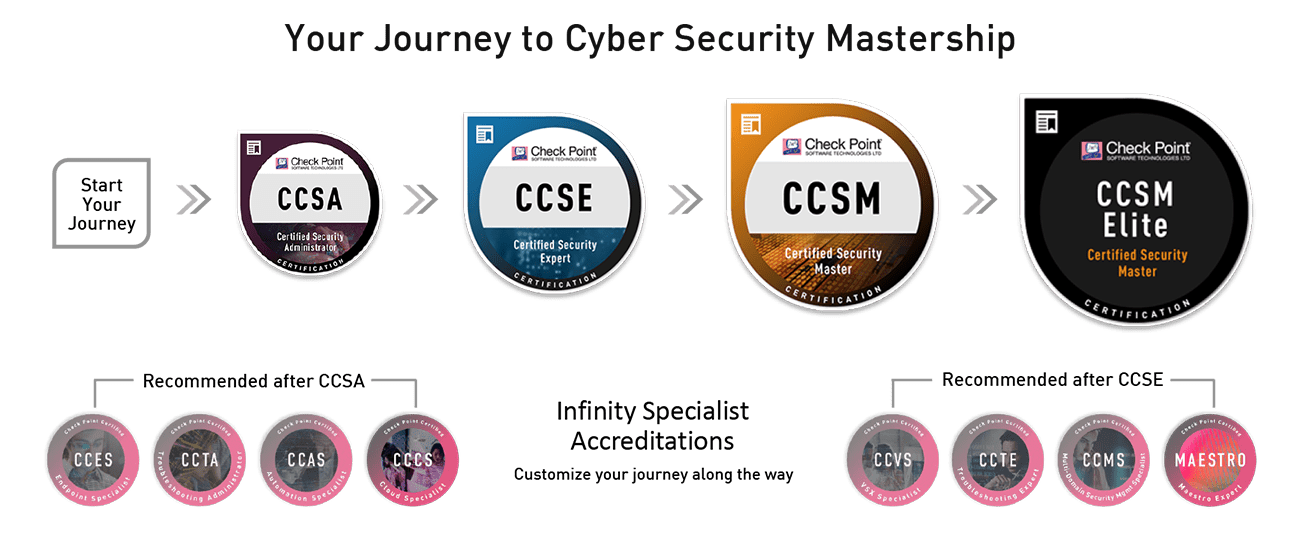
Курсът подготвя за следните сертификационни нива
-
156-315.80 – Check Point Certified Security Expert (CCSE) R80.x
- След този курс може да се сертифицирате в нашия тест център с безплатен ваучер.
Course Objectives:
Perform an upgrade of a Security Management server in a distributed environment.
Use the migrate_export command to prepare to migrate a Security Management Server.
Deploy a Secondary Management Server.
Demonstrate how to define new network and group objects using the Check Point API.
Perform an upgrade of Security Gateways in a clustered environment.
Use Kernel table commands to evaluate the condition of a Security Gateway.
Use common commands to evaluate the condition of a Security Gateway.
Configure Virtual MAC.
Demonstrate how SecureXL affects traffic flow.
Describe how the CoreXL acceleration technology enhances and improves Security Gateway performance.
Demonstrate how to monitor and adjust interface traffic queues.
Identify specific threat protections used by Check Point Threat Prevention.
Demonstrate how to enable Mobile Access for remote users.